From thehackernews.com
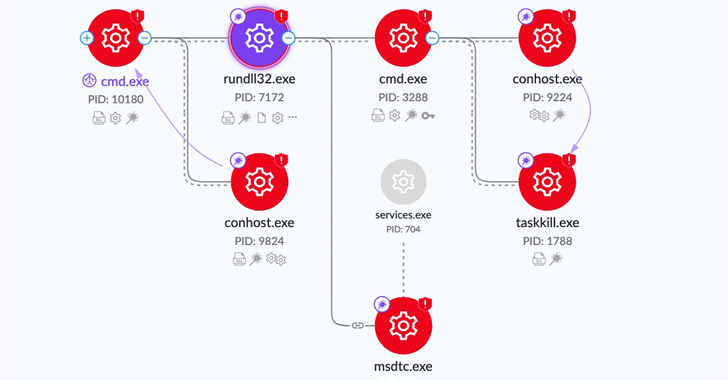
The threat actors behind the CatB ransomware operation have been observed using a technique called DLL search order hijacking to evade detection and launch the payload.
CatB, also referred to as CatB99 and Baxtoy, emerged late last year and is said to be an “evolution or direct rebrand” of another ransomware strain known as Pandora based on code-level similarities.
It’s worth noting that the use of Pandora has been attributed to Bronze Starlight (aka DEV-0401 or Emperor Dragonfly), a China-based threat actor that’s known to employ short-lived ransomware families as a ruse to likely conceal its true objectives.
One of the key defining characteristics of CatB is its reliance on DLL hijacking via a legitimate service called Microsoft Distributed Transaction Coordinator (MSDTC) to extract and launch the ransomware payload.