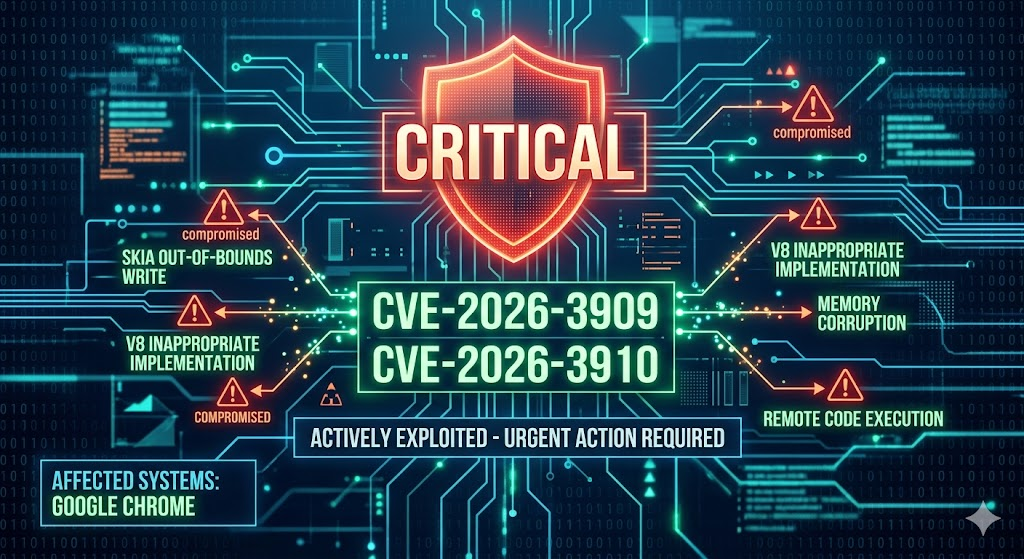
There have been two high-severity zero-day vulnerabilities identified in Google Chrome that are confirmed to be actively exploited in the wild. These flaws allow attackers to execute malicious code or gain unauthorized memory access simply by tricking a user into visiting a compromised website.
- CVE-2026-3909 (Out-of-bounds write in Skia): A flaw in the graphics engine that can lead to memory corruption and potential code execution.
- CVE-2026-3910 (Inappropriate implementation in V8): A vulnerability in the JavaScript/WebAssembly engine allowing arbitrary code execution within the browser sandbox.
Impact
A remote attacker can leverage these vulnerabilities to compromise your device, steal sensitive data, or install malware. Because Chrome is a primary tool for university work and SaaS applications, these flaws represent a significant risk to personal and institutional information security.
Required Action
Staff and students are advised to manually trigger an update for their Chrome browser immediately.