From thehackernews.com
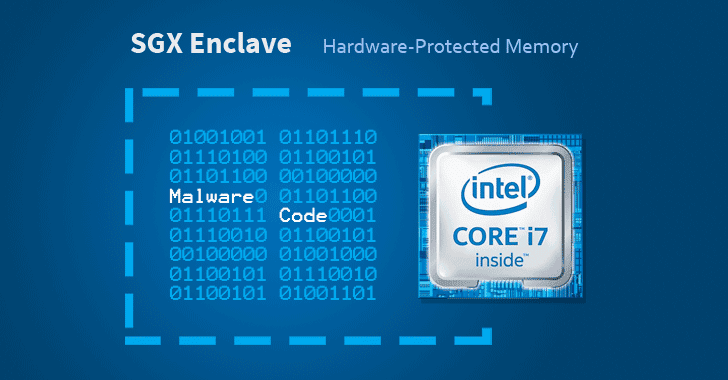
Cybersecurity researchers have discovered a way to hide malicious code in Intel SGX enclaves, a hardware-based memory encryption feature in modern processors that isolates sensitive code and data to protect it from disclosure or modification.
In other words, the technique allows attackers to implant malware code in a secure memory that uses protection features of SGX which are otherwise designed to protect important data from prying eyes or from being tampered, even on a compromised system.
Introduced with Intel’s Skylake processors, SGX (Software Guard Extensions) allows developers to run selected application modules in a completely isolated secure region of memory, called enclaves, which are designed to be protected from processes running at higher privilege levels like the operating system, kernel, BIOS, SMM, hypervisor, etc.