From helpnetsecurity.com
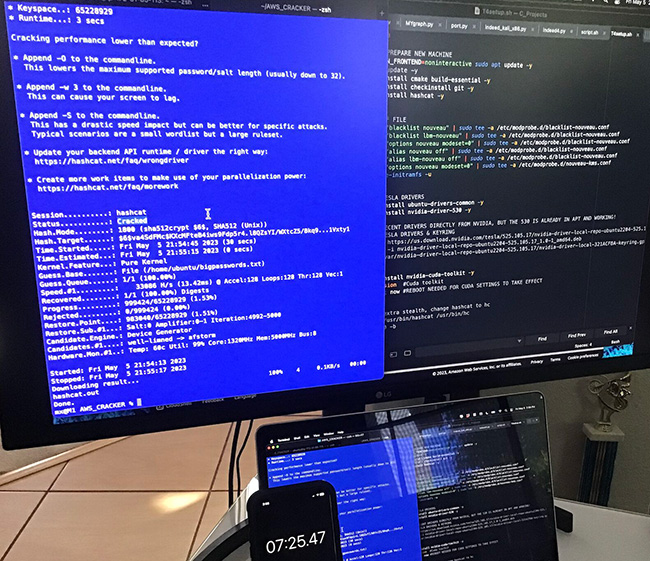
Building a custom cracking rig for research can be expensive, so penetration tester Max Ahartz built one on AWS. In this Help Net Security interview, he takes us through the process and unveils the details of his creation.
What motivated you to undertake this project, and what were your objectives in creating the automated cracking rig?
I embarked on this project with a dual motivation: my interest in automation and my recent exploration of AWS Cloud Penetration testing through Rhino Security’s Cloudgoat project. Combining these passions, I aimed to create an automated cracking rig to delve deeper into hash cracking.
What potential ethical considerations arise when working on a project like this? How do you approach the responsible use of the technology you’ve developed?
While the tools I utilized for this project have been well-established in the security community for over a decade, addressing the ethical considerations is crucial. I would say that responsible use is paramount. I have included a disclaimer emphasizing that the rig is intended solely for research. Users should ensure that the hashes used are either their own or self-generated.
Additionally, when working with clients to test their password security policies, obtaining explicit permission is essential to comply with legal and ethical obligations.