From 2-spyware.com
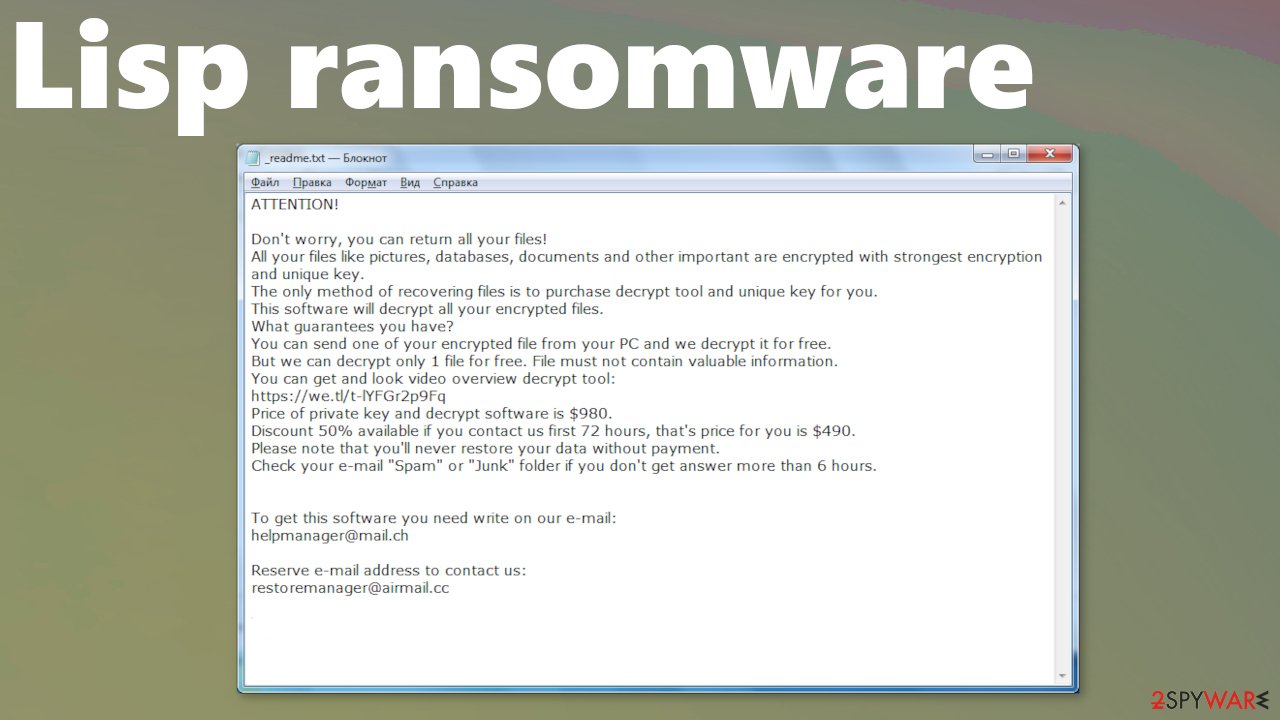
Lisp ransomware encrypts all non-system data after gaining entry to a computer and then asks for a ransom to unlock the files. This virus works like all ransomware before it. It has two phases – renaming all files by appending an extension and encrypting[1] them, and ransom note generation and placement.
Lisp ransomware virus derives from the ever-growing Djvu family, which consists of more than 260 viruses so far (Sglh, Epor, Agho, to name just a few). First versions were spotted in December of 2018, and new variants are introduced each week. All latest versions are using RSA[2] military-based algorithms to encrypt victim data.