From malware.news
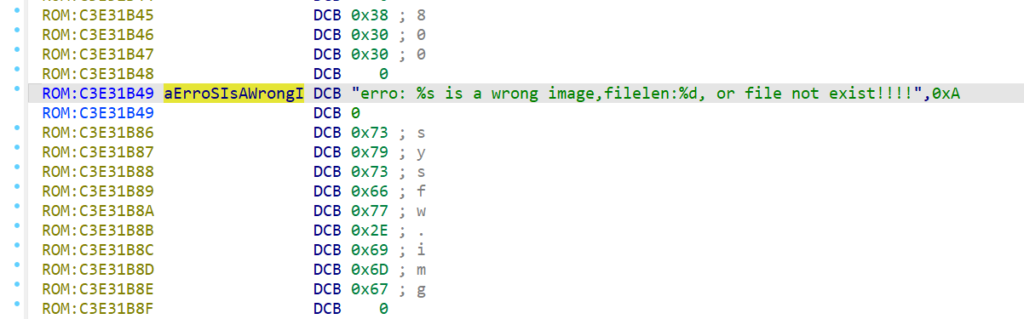
When analyzing firmware or other binaries without metadata, IDA is not always able to discover and analyze all functions which means the cross-references can be missing. Let’s say you found a string in the binary (e.g. in the String list) which has no cross references, but you’re reasonably sure it’s actually used. How to discover where?