From thehackernews.com
While it’s a norm for phishing campaigns that distribute weaponized Microsoft Office documents to prompt victims to enable macros in order to trigger the infection chain in the background, new findings indicate that macro security warnings can be disabled entirely without requiring any user interaction and infect victims’ computers with malware.
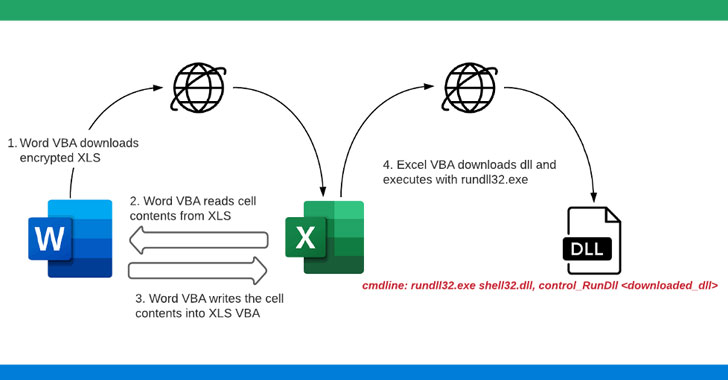
In yet another instance of malware authors continue to evolve their techniques to evade detection, researchers from McAfee Labs stumbled upon a novel tactic that “downloads and executes malicious DLLs (ZLoader) without any malicious code present in the initial spammed attachment macro.”