From securityonline.info
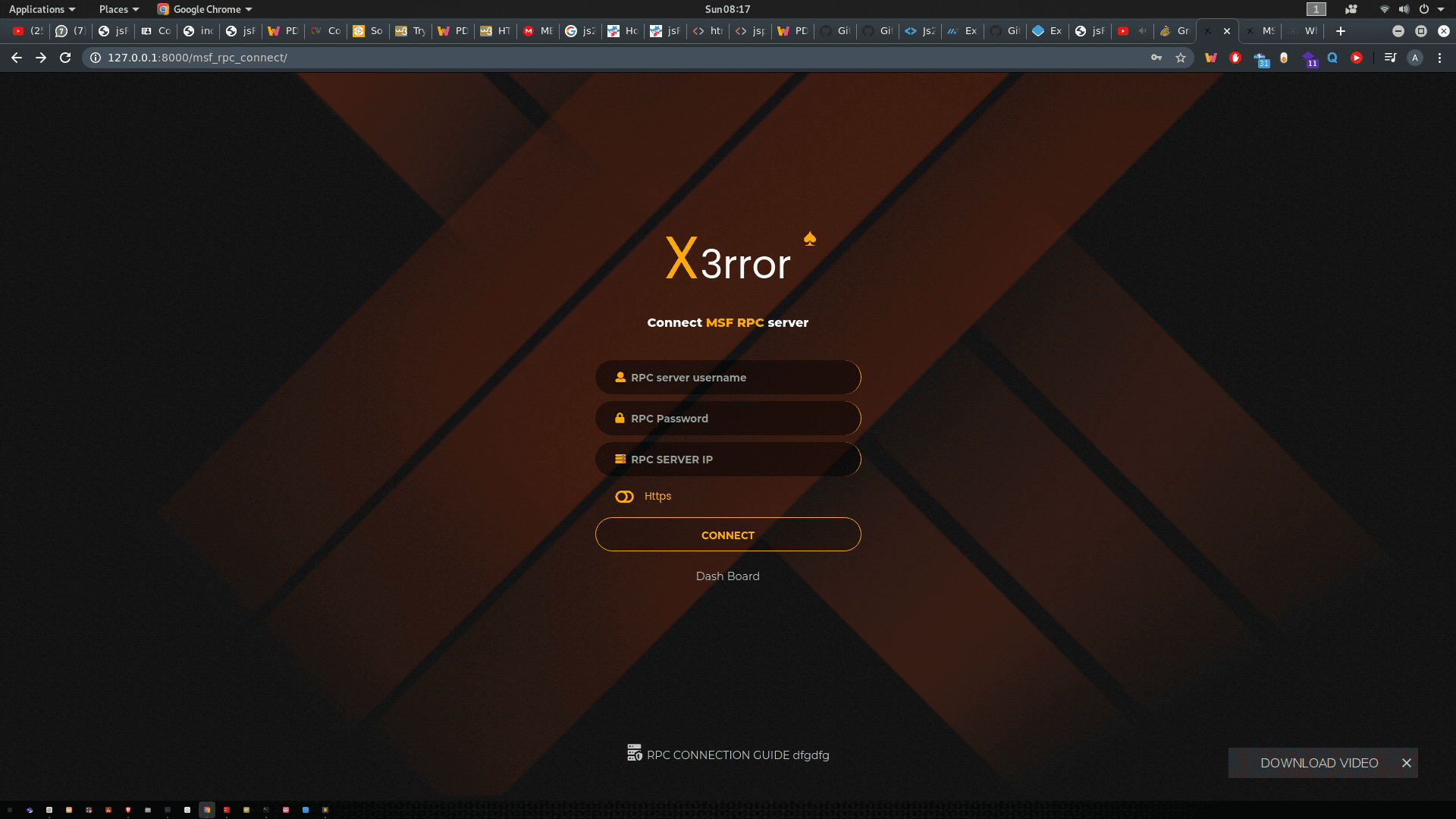
Xerror is an automated penetration tool, which will helps security professionals and nonprofessionals to automate their pentesting tasks. Xerror will do all tests and, at the end generate two reports for executives and analysts.