From theregister.co.uk
A company’s internal network, once compromised, is now more likely to be ransacked by automated scripts than a piece of malware.
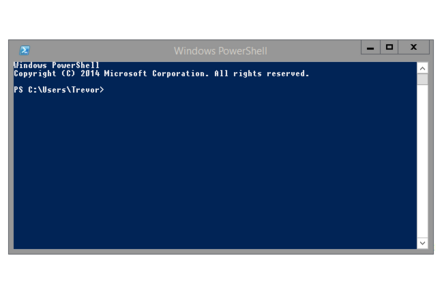
This according to researchers with IBM’s X-Force, who found that in 2018 just 43 per cent of the attacks it analyzed utilized any sort of locally installed files. Rather, the hackers utilized PowerShell scripts to execute their dirty deeds in memory without significantly touching file systems, if at all.
This finding is important because it is another reminder that admins can no longer solely rely on specific file signatures or similar as evidence of a cyber-intrusion. As with local malware infections, the attacker first needs to get the ability to run malicious commands. What differs is the next step, as the miscreant does not direct the infected machine to download, save, and execute a trojan payload.
Rather, the attack runs entirely as commands from PowerShell, where the powerful scripting language can be used to do anything from harvest and steal passwords to mine cryptocurrency.