From securityonline.info
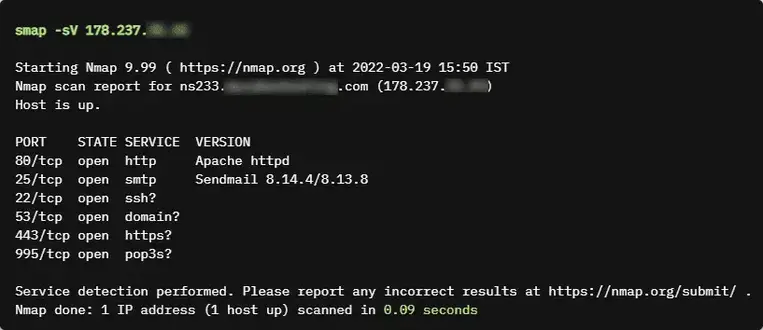
Smap is a replica of Nmap which uses shodan.io’s free API for port scanning. It takes the same command-line arguments as Nmap and produces the same output which makes it a drop-in replacement for Nmap.
From securityonline.info
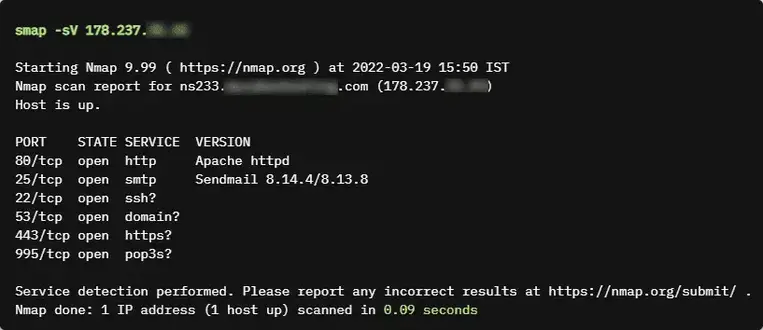
Smap is a replica of Nmap which uses shodan.io’s free API for port scanning. It takes the same command-line arguments as Nmap and produces the same output which makes it a drop-in replacement for Nmap.