From trendmicro.com
Update: As of July 17, the Pakistani government agency in question has found no compromise of its build environment. As the MSI installer file is not signed, we cannot remove the possibility that the threat actor obtained the legitimate installer and modified it to add the malicious files found in our analysis, and that users were lured to run this Trojanized version via social engineering attacks. They are currently carrying out a detailed forensic analysis of their systems to thoroughly investigate this incident.
However, we also note that the legitimate installer was not publicly available at the time of the incident (late September 2022). In addition, two different entities were compromised two days apart in this incident.
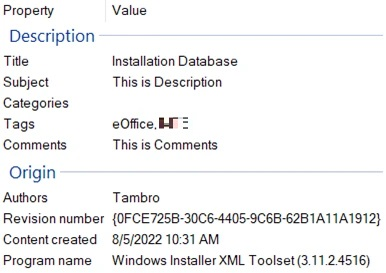
We recently found that an MSI installer of the Pakistani government app E-Office delivered a Shadowpad sample, suggesting a possible supply-chain attack.
Shadowpad is an advanced malware family that was discovered in 2017 after a supply-chain attack on a popular piece of server management software attributed to APT41. Since 2019, this malware has been shared among multiple Chinese threat actors such as Earth Akhlut or Earth Lusca.
The sample that was delivered implemented an updated version of the obfuscation technique discussed by PTSecurity in January 2021.