From thehackernews.com
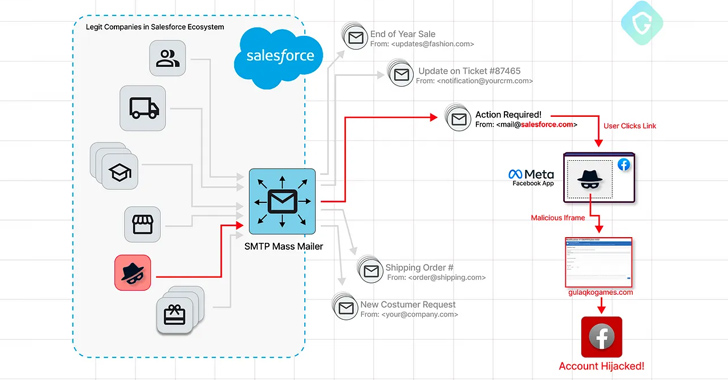
A sophisticated Facebook phishing campaign has been observed exploiting a zero-day flaw in Salesforce’s email services, allowing threat actors to craft targeted phishing messages using the company’s domain and infrastructure.
“Those phishing campaigns cleverly evade conventional detection methods by chaining the Salesforce vulnerability and legacy quirks in Facebook’s Web Games platform,” Guardio Labs researchers Oleg Zaytsev and Nati Tal said in a report shared with The Hacker News.
The email messages masquerade as coming from Meta, while being sent from an email address with a “@salesforce.com” domain. They seek to trick recipients into clicking on a link by claiming that their Facebook accounts are undergoing a “comprehensive investigation” due to “suspicions of engaging in impersonation.”
The goal is to direct users to a rogue landing page that’s designed to capture the victim’s account credentials and two-factor authentication (2FA) codes. What makes the attack notable is that the phishing kit is hosted as a game under the Facebook apps platform using the domain apps.facebook[.]com.