From thehackernews.com
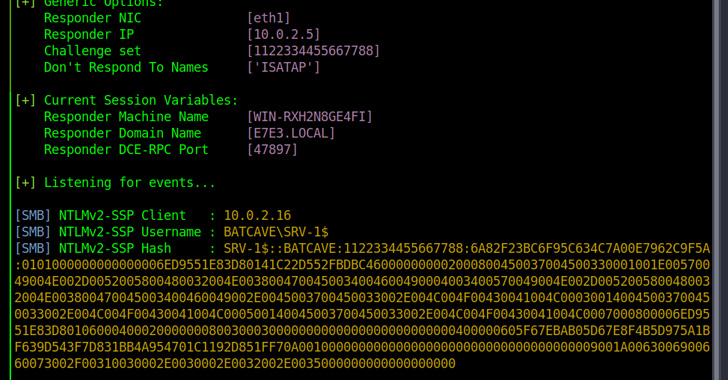
A new kind of Windows NTLM relay attack dubbed DFSCoerce has been uncovered that leverages the Distributed File System (DFS): Namespace Management Protocol (MS-DFSNM) to seize control of a domain.
“Spooler service disabled, RPC filters installed to prevent PetitPotam and File Server VSS Agent Service not installed but you still want to relay [Domain Controller authentication to [Active Directory Certificate Services]? Don’t worry MS-DFSNM have (sic) your back,” security researcher Filip Dragovic said in a tweet.
MS-DFSNM provides a remote procedure call (RPC) interface for administering distributed file system configurations.