From trendmicro.com
In June 2023, Trend Micro observed an upgrade to the evasion techniques used by the Batloader initial access malware, which we’ve covered in previous blog entries. The group behind Batloader (which we named Water Minyades) have begun employing Pyarmor Pro — a more sophisticated version of the regular Pyarmor protector command-line tool — to obfuscate its main malicious python scripts. Batloader previously used the standard version of Pyarmor, which can be manually de-obfuscated using open-source scripts. Water Minyades had been using Pyarmor since December 2022, likely since many antivirus engines lack an unpacker engine for Pyarmor (even the non-pro variant), making it difficult to detect these kinds of scripts.
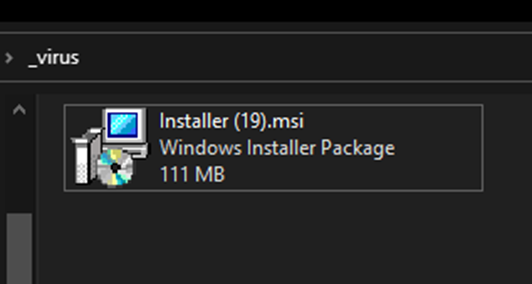
Aside from this unique evasion technique, Batloader also uses a variety of other techniques to make it more difficult to detect. One example of this is the use of large MSI files as a delivery vessel. Figure 1 shows an example of this, with a 111MB Batloader MSI file.