From securityboulevard.com
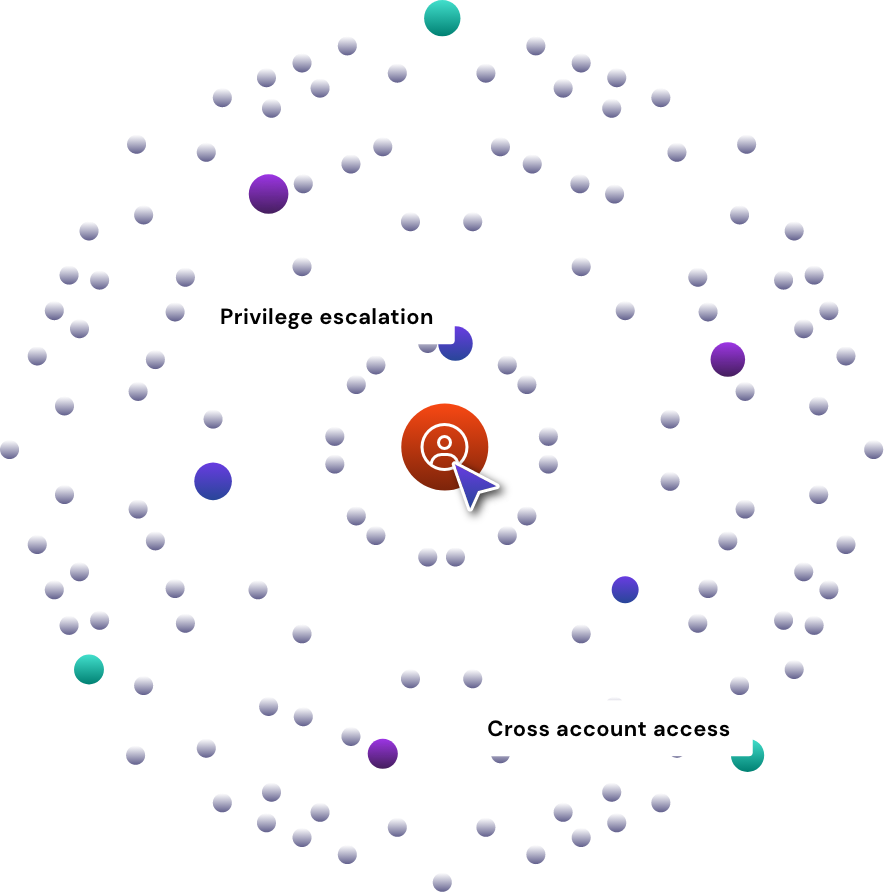
Beyond learning what privilege escalation is – an identity, whether it is a user or piece of compute, gaining access to rights or privileges beyond what’s intended for their level of access – is graduating to the question, “How do I detect privilege escalation in my cloud?” Before we address this question, we need to shed some light on the background behind this modern challenge.
What I often see at Sonrai are customers who are ready to secure their organizations, but they’re speaking the language of firewalls, antivirus, endpoint protection, and vulnerability scanning. A point we’ll make time and time again is that public cloud infrastructure is entirely different from on-prem. Because of this, Information security needs to be reimagined to suit this new world. If you’re not focused on identity and access controls, then you are blind to today’s threat landscape.