From helpnetsecurity.com
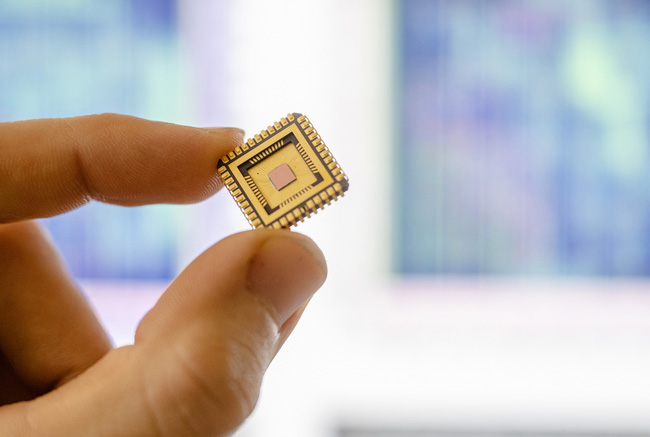
Not only do security vulnerabilities lurk within software, but they can also be embedded directly into hardware, leaving technical applications open to widespread attack.
Researchers from Ruhr University Bochum, Germany, and the Max Planck Institute for Security and Privacy (MPI-SP) are pioneering innovative detection techniques to combat these hardware Trojans. Their advanced algorithm can identify discrepancies by comparing chip blueprints with electron microscope images of the actual chips. This groundbreaking method successfully detected irregularities in 37 out of 40 cases.