From d3security.com
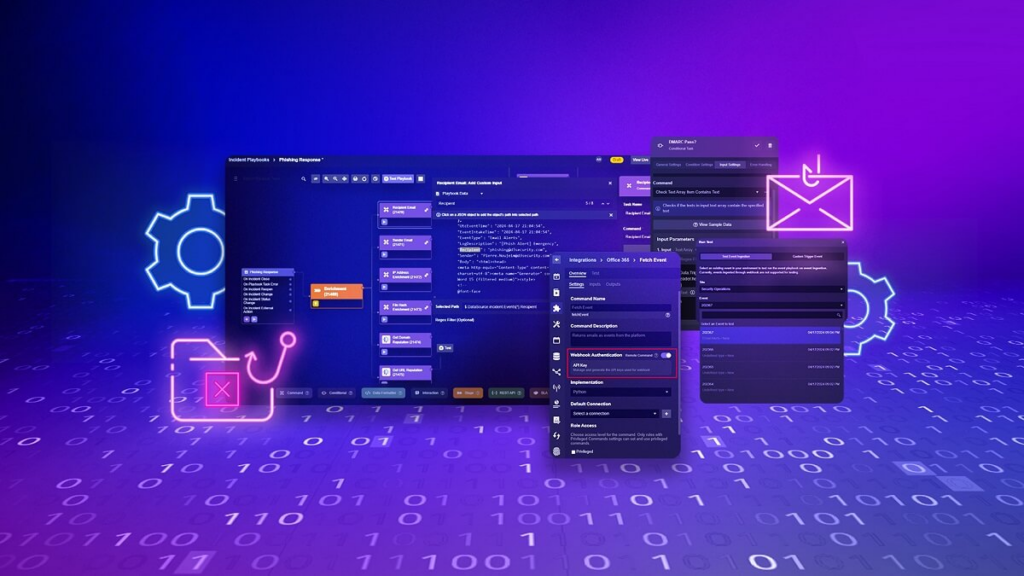
Welcome to the fourth and final part of our How to build a Phishing Playbook series. If you haven’t read the other parts, take a look using the links below. In this part we’ll be running test data through our playbook, filling out the dynamic inputs, then publishing it to production.