From malwarebytes.com
Malvertising seems to be enjoying a renaissance as of late, whether it is from ads on search engine results pages or via popular websites. Because browsers are more secure today than they were 5 or 10 years ago, the attacks that we are seeing all involve some form of social engineering.
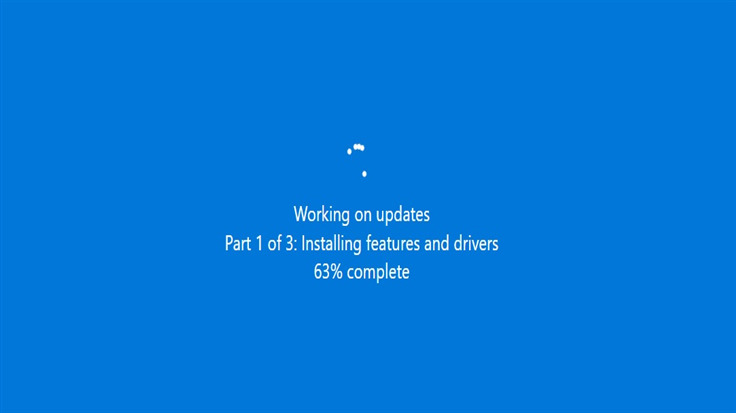
A threat actor is using malicious ads to redirect users to what looks like a Windows security update. The scheme is very well designed as it relies on the web browser to display a full screen animation that very much resembles what you’d expect from Microsoft.
The fake security update is using a newly identified loader that at the time of the campaign was oblivious to malware sandboxes and bypassed practically all antivirus engines. We wrote a tool to ‘patch’ this loader and identified its actual payload as Aurora stealer. In this blog post, we detail our findings and how this campaign is connected to other attacks.