From thehackernews.com
Cybersecurity researchers have discovered a case of privilege escalation associated with a Microsoft Entra ID (formerly Azure Active Directory) application by taking advantage of an abandoned reply URL.
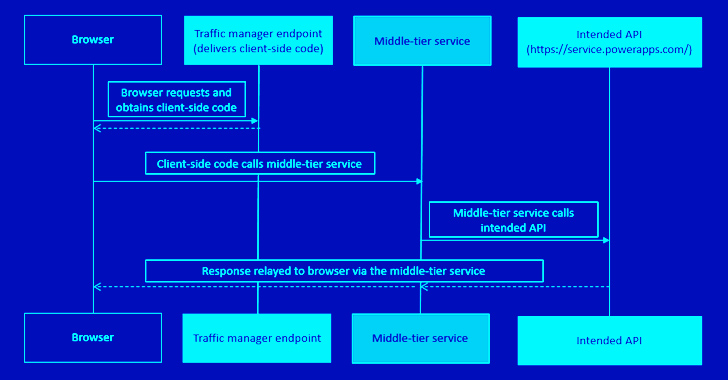
“An attacker could leverage this abandoned URL to redirect authorization codes to themselves, exchanging the ill-gotten authorization codes for access tokens,” Secureworks Counter Threat Unit (CTU) said in a technical report published last week.
“The threat actor could then call Power Platform API via a middle-tier service and obtain elevated privileges.”
Following responsible disclosure on April 5, 2023, the issue was addressed by Microsoft via an update released a day later. Secureworks has also made available an open-source tool that other organizations can use to scan for abandoned reply URLs.