From securityonline.info
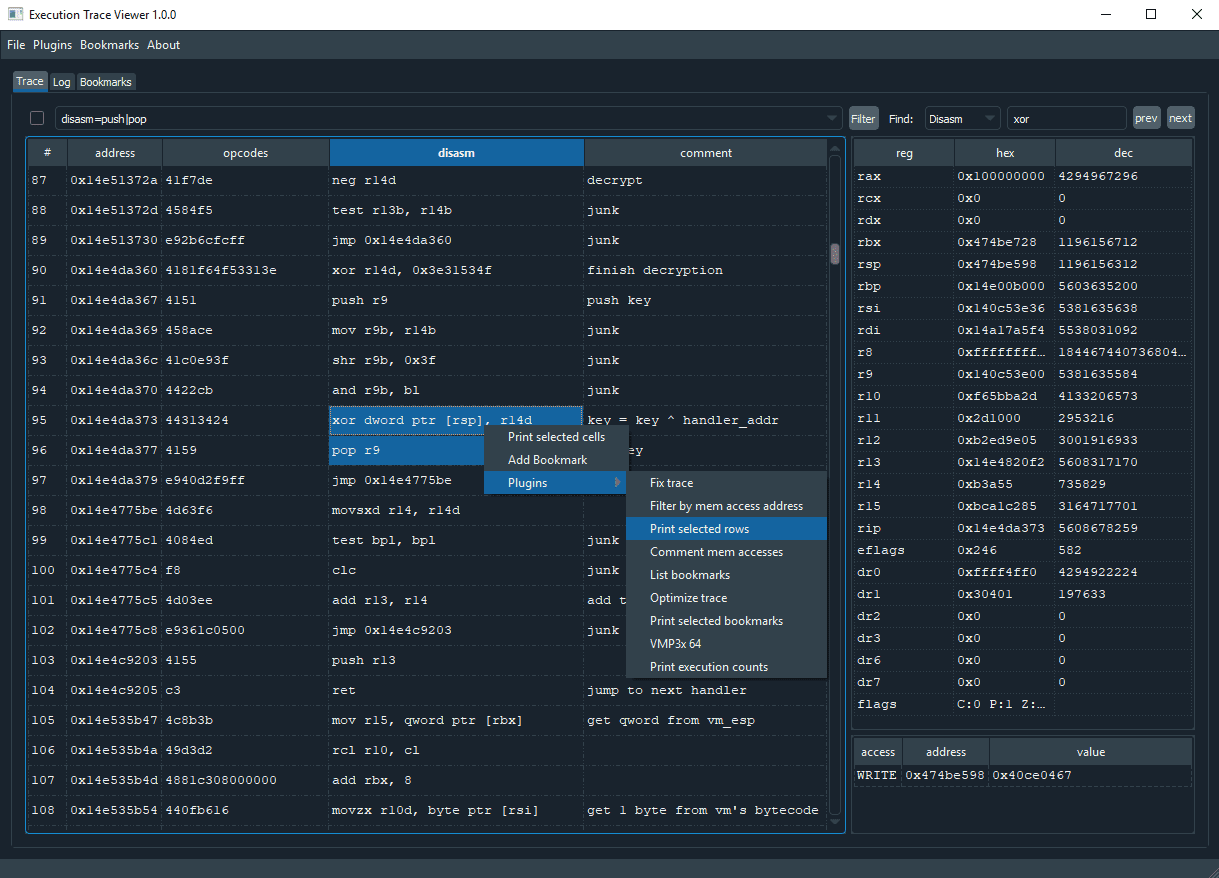
Execution Trace Viewer is an application for viewing, editing and analyzing execution traces. It was originally made for reverse engineering obfuscated code, but it can be used to analyze any kind of execution trace.
Execution Trace Viewer can be extended by Python3 plugins. Plugins are launched from the plugins menu or from the right-click menu on the trace table.
Check the example plugins and core/api.py for more info.