From securityaffairs.com
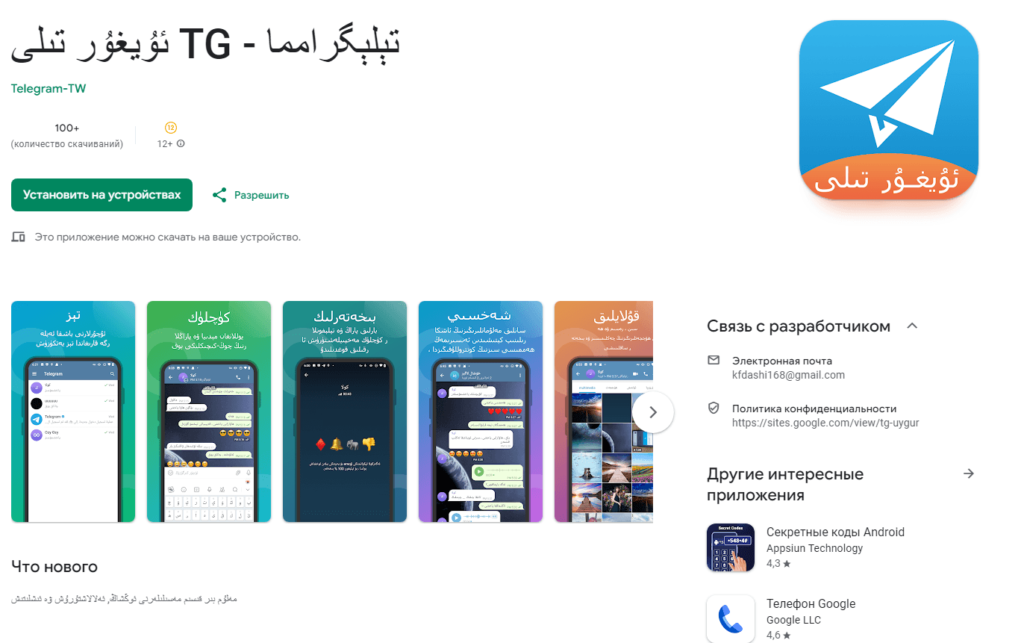
The trojanized apps were uploaded with descriptions in traditional Chinese, simplified Chinese and Uighur. The vendor advertised the applications are the fastest apps that use a distributed network of data processing centers around the world.
The malicious code hidden in the apps can harvest sensitive information from compromised Android devices.
The apps can collect information about the user’s contacts, including IDs, nicknames, names, and phone numbers.
The analysis of the code revealed that most packages of the trojanized version of Telegram look the same as the standard ones. However, Kaspersky experts noticed a package called com.wsys which is not included in the code of the legitimate Telegram. The package includes the code to steal sensitive data and process the incoming message.
“When receiving a message, uploadTextMessageToService collects its contents, chat/channel title and ID, as well as sender’s name and ID. The collected information is then encrypted and cached into a temporary file named tgsync.s3. The app sends this temporary file to the command server at certain intervals.” reads the analysis published by Kaspersky.