From malware.news
Openfire is an open-source, real-time collaboration server based on the XMPP (Extensible Messaging and Presence Protocol) protocol. It facilitates instant messaging, group chat, and other real-time communication services. Openfire is popular for its flexibility, scalability, and robust security features. It is commonly used in organizations and educational institutions, and even as a foundation for building custom chat and collaboration applications. Its ease of use and extensive plugin support have contributed to its widespread adoption for both internal team communication and customer-facing chat solutions.
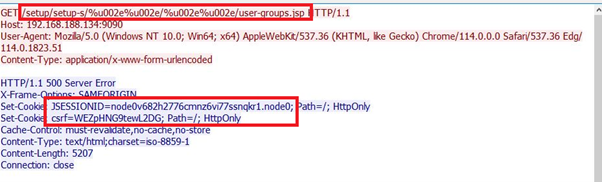
A recent discovery in May unveiled a fresh security concern (CVE-2023-32315) associated with the Openfire console. This vulnerability, characterized as a path traversal flaw, explicitly targets the setup environment. Exploiting this weakness empowers unauthorized users to compromise the unauthenticated Openfire Setup Environment within an established configuration. Subsequently, malicious actors can infiltrate admin setup files usually confined to the Openfire Admin Console’s access. This could lead to two significant actions: adding an admin user to the console or uploading a plugin, potentially securing complete control over the server.