From securityboulevard.com
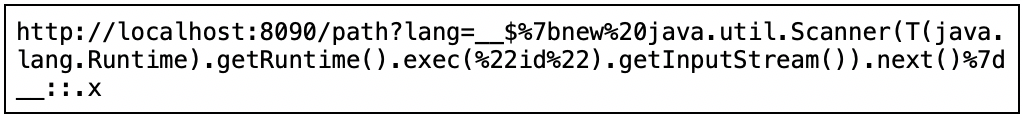
On September 4, 2020, Michael Stepankin published a proof-of-concept (PoC) exploit that took advantage of a fairly new application vulnerability dubbed “Spring View Manipulation.” The Spring View Manipulation vulnerability takes advantage of a recently discovered Thymeleaf Server-Side Template Injection (SSTI) vulnerability using Expression Language Injection. The PoC utilized Spring Boot to show how the vulnerability worked. The PoC allows malicious actors to create a specially crafted Expression Language injection payload to run local system commands. In the case of the PoC, the “id” command was run to return the local system user.