From asec.ahnlab.com
The seemingly state-sponsored Lazarus threat group has records of activity that date back to 2009. In the early days, their activities were mostly focused on Korea, but since 2016, the group has been attacking the defense, advanced technology, and finance sectors worldwide. The Lazarus group usually employed spear phishing and supply chain attacks, usually disguising the malware as legitimate programs in their attack process. [1]
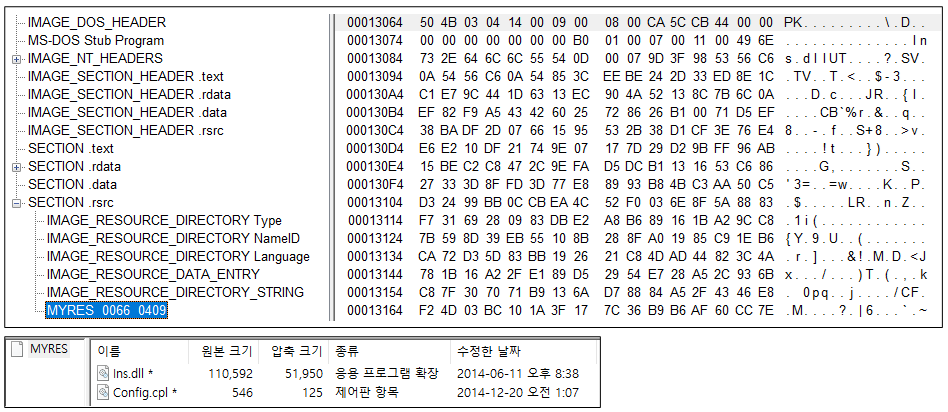
For the last few years, the group launched watering hole attacks to attack multiple Korean enterprises and organizations in the fields of defense, satellite, software, and media. Their method for initial access involved the exploitation of a security vulnerability of a Korean financial security certification software. [2] Even after initial access, the threat actor exploited vulnerabilities in web security software or enterprise asset management programs during lateral movement. [3] The Lazarus group attacks not only ordinary PCs but also server systems for the purpose of using them as malware distribution or C&C servers. [4] [5]