From thehackernews.com
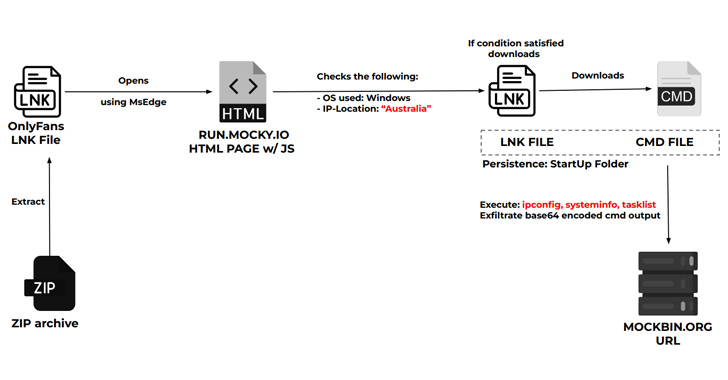
A new cyber attack campaign is leveraging the PowerShell script associated with a legitimate red teaming tool to plunder NTLMv2 hashes from compromised Windows systems primarily located in Australia, Poland, and Belgium.
The activity has been codenamed Steal-It by Zscaler ThreatLabz.
“In this campaign, the threat actors steal and exfiltrate NTLMv2 hashes using customized versions of Nishang’s Start-CaptureServer PowerShell script, executing various system commands, and exfiltrating the retrieved data via Mockbin APIs,” security researchers Niraj Shivtarkar and Avinash Kumar said.
Nishang is a framework and collection of PowerShell scripts and payloads for offensive security, penetration testing, and red teaming.