From securityaffairs.co
This week Apache Software Foundation has released HTTP Web Server 2.4.51 to address an actively exploited path traversal vulnerability (CVE-2021-41773) that was only partially addressed with a previous release.
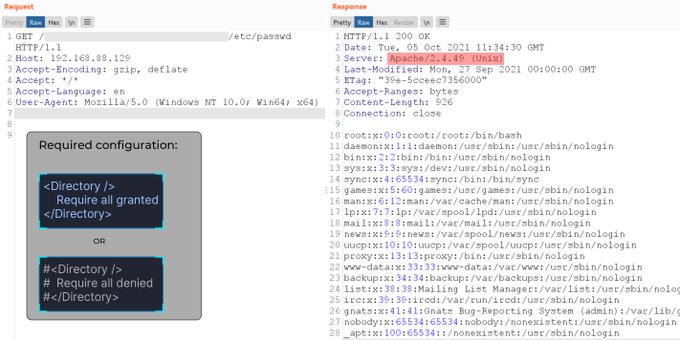
An attacker can trigger the flaw to map URLs to files outside the expected document root.
“A flaw was found in a change made to path normalization in Apache HTTP Server 2.4.49. An attacker could use a path traversal attack to map URLs to files outside the expected document root.” reads the advisory. “If files outside of the document root are not protected by “require all denied” these requests can succeed. Additionally this flaw could leak the source of interpreted files like CGI scripts.”
The vulnerability affects only version 2.4.49, earlier versions are not impacted. A few days ago, Apache released Apache HTTP 2.4.50 to address the CVE-2021-41773.