From techradar.com

- A huge dataset has been discovered unsecured online by researchers
- This contained roughly 4 billion records – including personal information
- The data could potentially be part of a surveillance effort targeting Chinese citizens
From techradar.com

Victims include hospitality, retail and education sectors
From theRegister.com

A group of financially motivated cyberscammers who specialize in Scattered-Spider-like fake IT support phone calls managed to trick employees at about 20 organizations into installing a modified version of Salesforce’s Data Loader that allows the crims to steal sensitive data.
Google Threat Intelligence Group (GTIG) tracks this crew as UNC6040, and in research published today said they specialize in voice-phishing campaigns targeting Salesforce instances for large-scale data theft and extortion.
From tomshardware.com
A cybersecurity expert has created a proof of concept for CPU ransomware.
Rapid7’s Chrstiaan Beek has written proof-of-concept code for ransomware that can attack your CPU, and warns of future threats that could lock your drive until a ransom is paid. This attack would circumvent most traditional forms of ransomware detection.
In an interview with The Register, Beek, who is Rapid7’s senior director of threat analytics, revealed that an AMD Zen chip bug gave him the idea that a highly skilled attacker could in theory “allow those intruders to load unapproved microcode into the processors, breaking encryption at the hardware level and modifying CPU behavior at will.”
from theregister.com
A group of miscreants tracked as UNC6032 is exploiting interest in AI video generators by planting malicious ads on social media platforms to steal credentials, credit card details, and other sensitive info, according to Mandiant.
The Google-owned threat hunters identified thousands of malicious ads on Facebook and about 10 on LinkedIn since November 2024. These ads directed viewers to more than 30 phony websites masquerading as legitimate AI video generator tools, including Luma AI, Canva Dream Lab, and Kling AI, falsely promising text- and image-to-video generation.
From bbc.com
The hackers behind a cyber-attack on Marks & Spencer (M&S) managed to gain entry through a third party who had access to its systems, the BBC understands.
The cyber-attack, which happened in April, has caused millions of pounds of lost sales for M&S and left it struggling to get services back to normal, with online orders paused for more than three weeks.
From welivesecurity.com
ESET analysts dissect a novel phishing method tailored to Android and iOS users.
[They] discovered a series of phishing campaigns targeting mobile users that used three different URL delivery mechanisms. These mechanisms include automated voice calls, SMS messages, and social media malvertising.
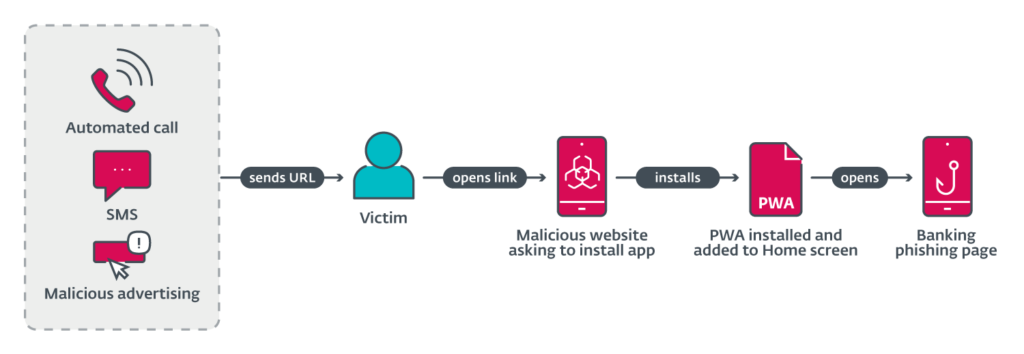
The voice call delivery is done via an automated call that warns the user about an out-of-date banking app and asks the user to select an option on the numerical keyboard. After pressing the correct button, a phishing URL is sent via SMS. This was reported in a tweet, by Michal Bláha.
Initial delivery by SMS was performed by sending messages indiscriminately to Czech phone numbers. The message sent included a phishing link and text to socially engineer victims into visiting the link.
From bleepingcomputer.com
Threat actors have hijacked more than 35,000 registered domains in so-called Sitting Ducks attacks that allow claiming a domain without having access to the owner’s account at the DNS provider or registrar.
In a Sitting Ducks attack, cybercriminals exploit configuration shortcomings at the registrar level and insufficient ownership verification at DNS providers.
Researchers at DNS-focused security vendor Infoblox and at firmware and hardware protection company Eclypsium discovered that there are more than a million domains that can be hijacked every day via the Sitting Ducks attacks.