From securityonline.info
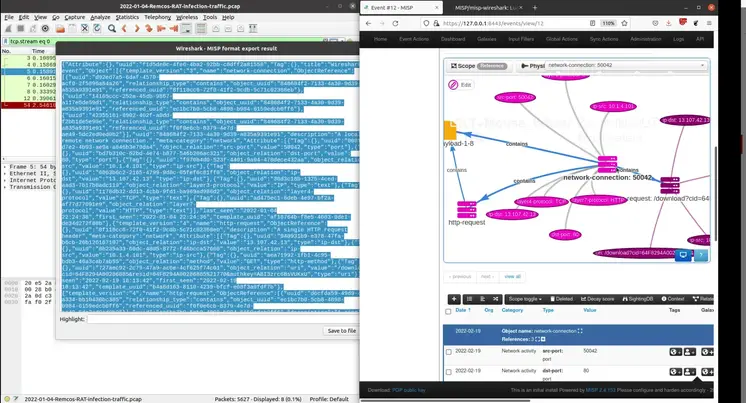
misp-wireshark is a Lua plugin intended to help analysts extract data from Wireshark and convert it into the MISP Core format.
From securityonline.info
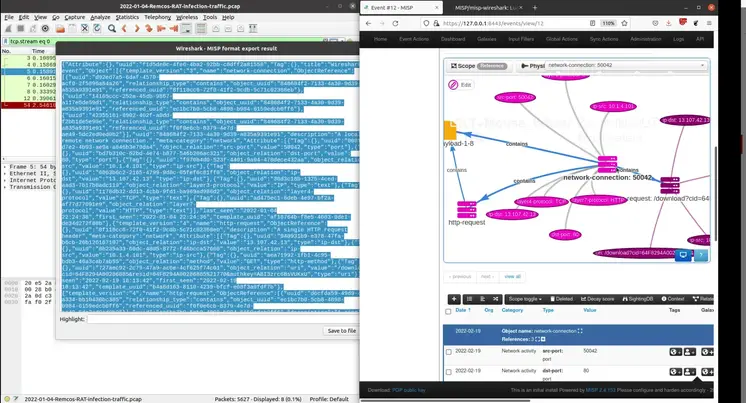
misp-wireshark is a Lua plugin intended to help analysts extract data from Wireshark and convert it into the MISP Core format.